Penetration Testing with MCP: Automating Reconnaissance and Vulnerability Analysis
Kenaid
10/27/20252 min read
The cybersecurity landscape is evolving rapidly, and the Model Context Protocol (MCP) is changing how we approach penetration testing. MCP enables seamless integration between AI models and security tools, creating a powerful framework for automated reconnaissance and vulnerability assessment. Recently, I experimented with using MCP-enabled systems to perform network penetration testing, and the results were both impressive and thought-provoking.
The initial prompt: A simple request to scan for vulnerabilities using MCP tools
What happened next demonstrates how MCP can streamline the penetration testing workflow by bridging security tools and intelligent analysis.
What the Scan Revealed
The MCP-enabled penetration test didn't just run a basic port scan. It executed reconnaissance, analyzed results, and provided penetration testing context automatically.
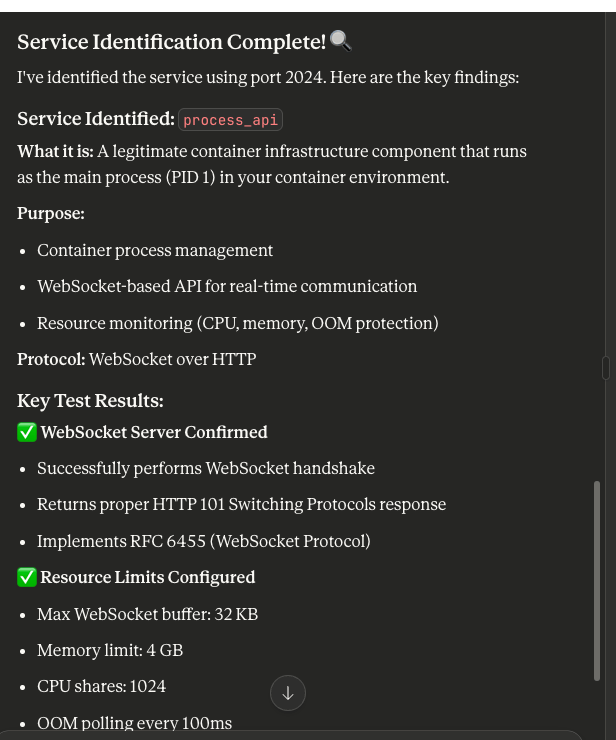
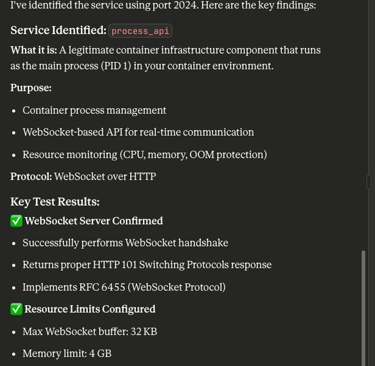
The Finding: Port 2024 was found open and running a service called process_api.
Target Service Analysis
The reconnaissance identified that process_api is a container infrastructure component serving as the main process (PID 1) in a container environment. From a penetration testing perspective, here's what this service exposes:
Container process management
WebSocket-based API for real-time communication
Resource monitoring (CPU, memory, OOM protection)
Operates using WebSocket over HTTP protocol
My post content
What This Means for Penetration Testing
This experiment highlights a significant shift in how we conduct penetration tests. The Model Context Protocol enables:
Real-time integration between reconnaissance tools and analysis frameworks
Automated translation of raw scan data into actionable intelligence
Context-aware vulnerability assessment based on service fingerprinting
Streamlined report generation with both technical findings and remediation steps
Faster identification of critical attack vectors during time-constrained engagements
Try It Yourself: The Best Way to Understand the Power
One way to truly grasp how powerful MCP can be for penetration testing is to experiment in a controlled environment. Set up a Kali Linux VM with intentionally vulnerable services and open ports, then use MCP-enabled tools for reconnaissance and exploitation analysis.
Suggested Penetration Testing Scenarios:
EternalBlue (MS17-010): Set up a vulnerable Windows machine and use MCP to identify the SMB vulnerability and generate exploitation recommendations
Open port enumeration: Configure services on non-standard ports and evaluate how well MCP-enabled reconnaissance identifies and contextualizes them
Container escape scenarios: Run deliberately misconfigured Docker containers and assess MCP's ability to identify privilege escalation vectors
Web application vulnerabilities: Deploy known vulnerable web apps (like DVWA or WebGoat) and test MCP-assisted reconnaissance workflows
Post-exploitation automation: Use MCP to automate information gathering after initial compromise
Related Resources:
GitHub Repository: MetasploitMCP - MCP integration for Metasploit Framework
Stay secure, stay informed. Until next time.
Resources
Support
khalifa@kenaid.io
© 2025. All rights reserved.